 Famous marketing guru Peter Drucker once said –
Famous marketing guru Peter Drucker once said –
“Businesses Exist to Create Customers.”
While that paradigm has been true for generations, today even he may agree if we say –
“Businesses Exist to Create Customers… Who Create Customers”.
In his book – Social Physics, How Good Idea Spread – Lessons from A New Science – Prof Alex Pentland from MIT argues that human behavior can be best predicted by social context in which people operate. Ideas and behavior spread from social contacts much more than any direct influence. Social context can predict with remarkable accuracy, how people might act.
There are academic research papers which prove in many contexts that direct influence is at least twice as expensive as social influence.
If you think about this, it has profound impact on marketers. All the traditional marketing methods are based on how you convince your prospect to buy your product. Web content, display and search ads, email marketing – all are geared towards this. Even when most marketers think of social marketing, they think of advertisements on Facebook, Facebook page engagement or Twitter following. As you can see, even when we engage in “social marketing” in these ways, we are not truly leveraging the power of social physics.
We of course have several other studies such as the one below confirming this point of view for a while.
Leveraging Social Physics in Marketing
Leveraging social physics for marketing requires a completely different mindset. It requires understanding how your prospects are related in social world to your existing customers and how you can create incentives and mechanisms for your existing customers to communicate to prospects the benefits of your products.
Thinking this way will require us to fundamentally think differently about how we market. Here is a table that summarizes some of the key differences between direct marketing and influence marketing (avoiding the term social marketing because it can be confused as explained above).
Understanding Customer and Prospect Network
Creating a data structure of customer relationships is a fairly complex problem. Traditionally, master data management tools are used to help with it. But these tools often prove insufficient in the new context. These tools often use match thresholds and deem any matches above a threshold as exact matches.
In fact, in real world, match thresholds tend to be guesses and therefore, probabilistic. Additionally, different probability thresholds can be sufficient for different types of use cases. For example, match probability of 60% and above may be enough for many direct marketing use cases, but you better have match probability of over 90% for compliance audits.
A more modern way to model customers may be to use graph modeling techniques. Think of each node of the graph as a customer interaction and each link telling you about probability. You can determine this probability through algorithmic scoring.
 For example, here is a case of two devices used by the same customer. Based on ip address, location and time analysis, one can make out that this is likely the same person. Additionally, one can guess with some probability what this person’s home and office ip addresses are.As next step then, one can link this identity to other devices. For example, this person goes home and uses iPad and iMac which you can associate with the identity using IP address link. Additionally, even though the iMac is shared between this person and their spouse, you can conduct similar algorithmic analysis to separate browsing behavior on the same device across two persons. You can also flag them as being part of the same household. Similarly, you can flag other devices on the work ip address as being part of the same company.
For example, here is a case of two devices used by the same customer. Based on ip address, location and time analysis, one can make out that this is likely the same person. Additionally, one can guess with some probability what this person’s home and office ip addresses are.As next step then, one can link this identity to other devices. For example, this person goes home and uses iPad and iMac which you can associate with the identity using IP address link. Additionally, even though the iMac is shared between this person and their spouse, you can conduct similar algorithmic analysis to separate browsing behavior on the same device across two persons. You can also flag them as being part of the same household. Similarly, you can flag other devices on the work ip address as being part of the same company.
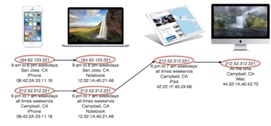 You can take this logic further. If your company has a way for this person to login to your website, you can associat
You can take this logic further. If your company has a way for this person to login to your website, you can associat
e the identity graph created so far to a name, email and other specific information. You can also associate it with internal offline data such as purchase history, support case history etc.
Additionally, you could leverage social sign-ons. For example, if this person signs up with his/her Facebook account, you could associate his social graph with his identity. You could then associate these “friends” with their other behavior – site visits, fan page likes etc. to identify segment of these “friends” who might be interested in your products and that gives you a great data to build your influence marketing program on.
Finally, you can use this model to break down the wall between consumer and enterprise marketing. For example, if good number of employees of a company are using your product, you can market enterprise volume license to the company.
Health of Identity Graph
A model like this would succeed only when there are tools in place to monitor ongoing health and quality of the model. Other big consideration is the temporal quality of data – i.e. how do you adjust probabilities over time as the event driving the probability ages.
Another key consideration is the privacy policy. For example, if the user explicitly logs out, is it ok to maintain the connection between the anonymous and identified parts of the identity graph? In some jurisdictions, this will be against the law. It also raises other privacy policy considerations and a policy enforcement mechanism is important part of such database.